It looks like RFID tags may make it onto store shelves sooner than we had been led to believe. The industry had been trying to say that this could be as much as ten years away and that their current efforts were geared towards case and palette tracking. However, Wal-Mart is already running a trial with HP printers in the Dallas area. Additionally, a major national clothing retailer appears ready to bring this out as early as next year on all of their retail clothing items.
As I’ve mentioned before, I have serious privacy concerns about the use of RFID tags on individual items that we purchase. If it’s just on the packaging, and we throw away the packaging, that would probably be OK (which is what Wal-Mart claims is the case with the HP printers; Hmm… I still have my packaging from the last HP printer I bought, just in case I need to send it back, although I bought it at Fry’s). It’s when the RFID tag is embedded in the item and can’t be removed that things get nasty.
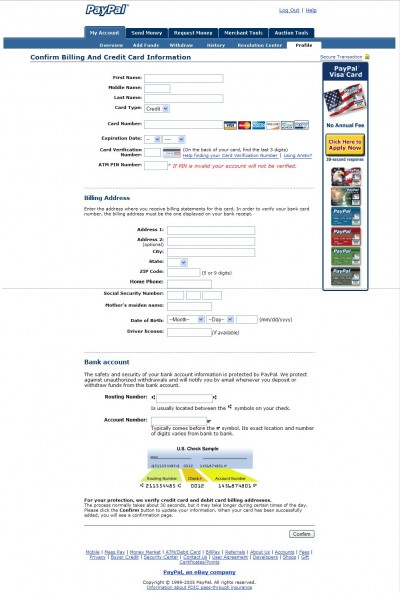
The problem with RFID tags is that they don’t just identify what something is (i.e. a particular brand/size of a known brand item), they also give a unique identifier for that instance of the object (a serial number). If you can read the tag to get the serial number and cross-reference that with sales data you can tell a lot about a person.
The RFID industry is desperate to debunk these “concerns” as not realistic or to reassure us that any purchase databases will be protected. Let’s examine the potential problems.
Privacy activists worry that consumers could leave stores broadcasting all kinds of information about their belongings. They fear that, with the right tools, anyone—including thieves—could detect what’s in your purse or pockets. Another concern is that people’s things would leave an electronic trail of their whereabouts and shopping habits for law enforcement officials, investigators, lawyers or marketers to collect.
RFID defenders say such concerns are overblown—a common theme at this conference. One argument is that the only information companies are interested in storing on RFID tags are serial numbers, which are meaningless without access to the database where all the information about the item lives. Only the privileged eyes of certain employees would have access to that database, executives say. Another argument is that RFID tags only submit signals only when prompted by a reader within close range, generally a few feet at most.
Concerning this database of serial numbers, I simply don’t trust these companies to run such a thing without the potential for privacy leaks. Further, even if they do manage to put in place a decent and effective privacy policy today, there’s nothing to stop them from changing the terms later on, after they’ve amassed a tremendous database (“I am altering the terms of our deal. Pray I do not alter them further.”). If you think I’m paranoid, you may want to revisit the original debates on the establishment of Social Security Numbers. People who were concerned about this were given assurances that the SSN would never be used for any purpose other than providing Social Security. Heck, it’s even in the law that the SSN is not to be used for identification purposes. That really did a lot of good, didn’t it?
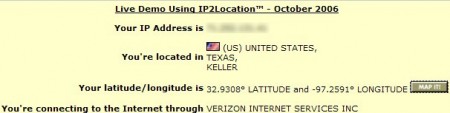
As noted above, the RFID industry claims that these tags can only be read from a few feet away. Even that’s not sufficient if you can get people to pass through some kind of chokepoint where they pass a few feet from a reader. Ever notice those vertical “dividers” placed between doors in most retail stores these days? Those are magnetic readers for current loss-prevention systems. That kind of chokepoint could be readily adapted for RFID purposes.
But even given that these devices are limited to short ranges today, how can we definitely say that there will never be technology capable of activating and reading the tag at greater ranges? I wouldn’t take that bet. I wonder if the original inventors of the CRT ever thought about van Eck Phreaking?
So, to sum it up, I don’t trust the companies to guard my privacy in the future with regard to the serial numbers of products I’ve purchased, and I don’t trust that technology won’t be found that allows reading the tags at longer ranges. However, there is a simple solution to my concerns. Simply kill the tags at the time of purchase.
Of course, the RFID industry is quick to resist this solution. They give a variety of reasons, but my suspicion is that they ultimately do want to be able to track everything at some point in the future (even if they won’t admit it to themselves).
Here’s their current set of excuses:
Retailers and consumer-goods companies are hesitant to agree to removing tags from items at the time of purchase for several reasons. One reason is that RFID tags could help with returns by exposing people trying to get a refund for a product they never really bought, or one they purchased from another store. In the future, technology proponents envision medicine cabinets and home appliances equipped with RFID readers, alerting people to expired drugs and automatically selecting the gentle cycle on the washing machine for delicate clothing.
Frankly, I don’t give a damn about these problems. I’m willing to pay the slightly higher prices that refund scams generate in exchange for privacy. Frankly, there are non-RFID methods for dealing with fraud, though, so I find this an unpersuasive point. As far as these “smart home” concepts, the industry’s own research shows that people don’t care about these things (although they keep hammering on this; in my more cynical moments I think they hope it will be the sugar that helps people to swallow RFIDs).
All the industry needs to do is make sure the tags are killable and that people are fully informed about how to make sure they’re dead before leaving the store. That one thing would mollify me. As long as they resist this, I will regard them with a high level of suspicion. Resisting what seems to me to be such a reasonable request makes me very wary of their ultimate motives.
Some previous items I’ve written on the subject of RFID tags:
The basic problem.
RFID and cameras.
Implanting RFID chips.
 December 20, 2006
|
Posted by Aubrey Turner
December 20, 2006
|
Posted by Aubrey Turner
 Categories:
Categories: